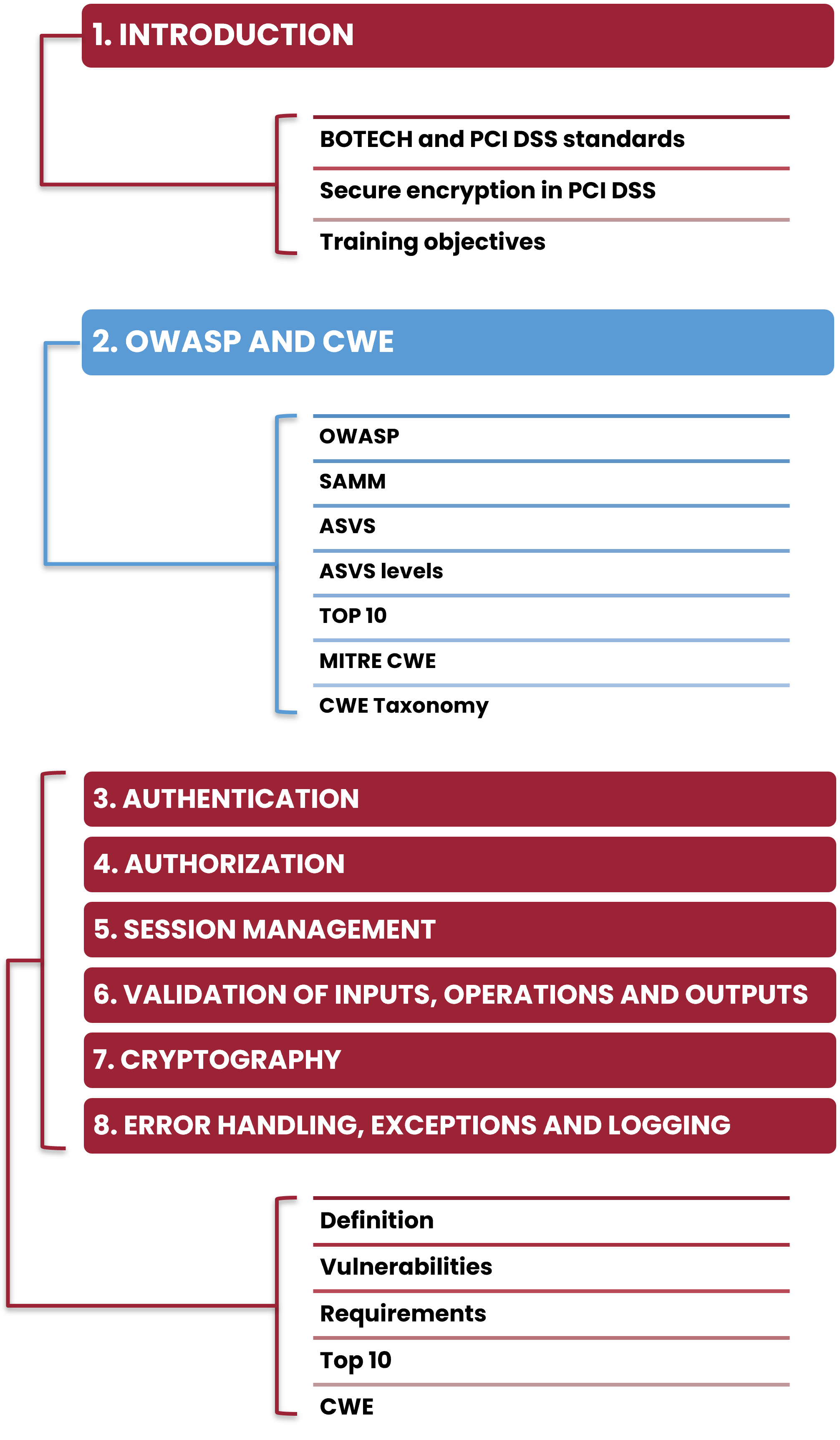
Training methodology oriented to Secure Development for companies that develop web applications that are subject to PCI DSS due to their own or their clients' requirements. With additional modules specific to programming languages, in compliance with version 4.0.1 of the standard.